What Is Email Spoofing, and How Can You Protect Yourself?
Table of Contents
- By Bryan Lee
- Published: Oct 23, 2023
- Last Updated: Mar 17, 2026

A subtype of a phishing scam, email spoofing is an attack meant to trick the recipient into trusting an email's legitimacy. It's estimated that scammers send over 3 billion spoofing emails daily, targeting people of all ages and social statuses.
With these numbers, you've undoubtedly had a spoofed email or two pop into your inbox and will again in the future. Recognizing and reacting to this attack is essential to protecting your online safety and identity.
What is Email Spoofing?
Spoofing is a broad definition for attacks in which the assailant hides their identity by impersonating a more trustworthy source. This tactic is effective in any communication channel that immediately informs the recipient of who's trying to reach them. Doing so creates an automatic sense of trust that dramatically raises the chances of the recipient sharing sensitive personal information.
In email spoofing, the scammer changes aspects like the display name or sender address. One of the scariest aspects of email spoofing is that the criminal doesn't need to take over the account they're impersonating. Spoofers abuse email domains' lack of security or use an email similar to a trustworthy source.
Differences Between Email Spoofing and Phishing
Email spoofing is just one phishing tactic criminals can use to steal sensitive information from people. Cyber professionals discuss these processes separately because the "nature and intent" behind them differ.
Phishing is a carefully calibrated social engineering attack focused on extracting information from victims. An email can't be considered a "phishing attack" if not done with malicious intent.
The act of email spoofing alone doesn't constitute fraud. The attacker hasn't stolen anybody's credentials, nor have they technically broken any rules. In the most naïve way to think about it, the spoofer coincidentally uses an email address similar to one of the victim's acquaintances.
It isn't until malicious content or intent is added to the email that spoofing crosses the line. However, this is a largely semantic point, and it's wise to think of all spoofed email addresses as threats similar to phishing.
Additionally, phishing is used exclusively to extract sensitive information from the victims, leading to identity theft, corporate espionage, or other consequences. Email spoofing has more specific benefits, making it a popular option for scammers.
Builds Trust with the Target
The main selling point of email spoofing is that the perpetrator leverages another entity's relationship with the target. Phishing typically relies on negative emotions like fear or stress to force a mistake or a lapse in judgment.
However, stolen identities for email spoofing are often positive, such as friends, coworkers, or family members. Varying the approach this way can help scammers avoid detection from people wary of traditional social engineering attacks.
Dodges Spam Filters and Blacklists
In recent years, there's been a strong push for increased protections from email providers. One of the most prominent security features is email blacklists. Blacklists are a database of IP addresses and domains that the provider automatically blocks.
If a domain or user is repeatedly recognized as sending spam, their information is added to the blacklist. Attackers can imitate an email address less likely to be flagged by the filter settings. This flexibility gives email spoofing better odds of making it to your inbox than other threats.
Damages the Reputation of the Presumed Sender
There's a reason why big corporations devote millions of dollars to public relations. A reputation is worth a lot, and just having a neutral image can be considered a win. Email spoofing has the potential to ruin reputations.
A fake email can hide many threats, including malware links, phony information, or plain old abusive language. Receiving any of these will make the recipient lose their faith in the sender, which could lead to lost business deals and professional relationships.
How Spoofing Works
There are many ways criminals can spoof an email. The simplest methods require next to no computer skills, while more complex tactics are more challenging to detect. Here's a breakdown of what you should watch out for in your inbox:
Display Name Spoofing
The display name is the text that appears in an email's "To:" field and is how the recipient first registers the sender's identity. Changing this information is as easy as creating a fresh email account under the desired name.
Since only the sender's name is changed with this method and not the email address itself. This is a double-edged sword since the attacker can tailor the address to bypass spam filters, but it also leaves an opening for the target to notice that the address doesn't match the name.
Also, most mobile interfaces and windowed email applications don't have the room to display the full email address in the inbox. These limitations mean recipients often only see the display name before clicking through.
Domain Spoofing
Domain spoofing is a much more under-the-radar approach and is typically done in tandem with display name spoofing. The attacker uses a legitimate website as the email address domain, which is possible because Simple Mail Transfer Protocols (SMTP) don't properly authenticate connections.
Currently, there are roughly six million SMTP servers ready for criminals to abuse. The good news is that new protocols like SPF, DKIM, and DMARC include measures to verify an email's origin against domain spoofing. You can verify if these protocols are correctly configured by running a free email deliverability test to ensure your domain isn't being exploited by bad actors.
Using a Lookalike Domain
Even newer protocols aren't entirely safe. Domain authentication prevents attackers from imitating legitimate domains, but nothing stops them from creating a NEARLY identical domain.
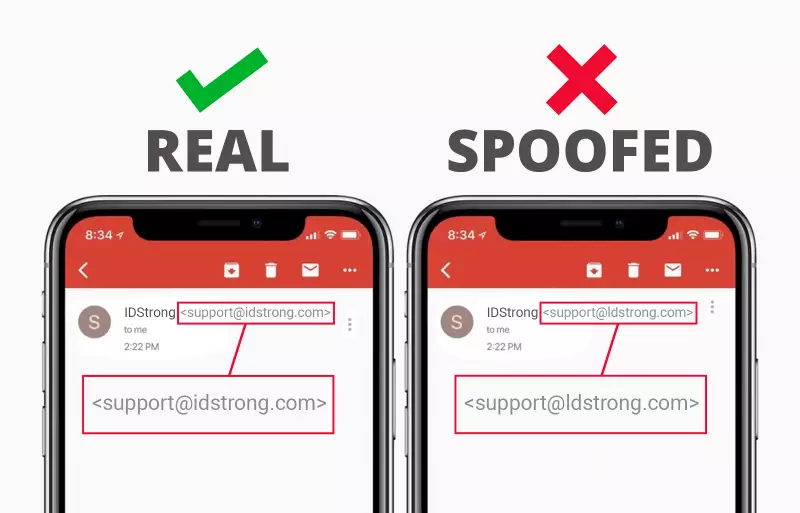
A lookalike appears identical to a legitimate domain aside from a small change. For example, if "@idstrong.com" is protected, then the fraudster would register a domain called "@idstr0ng.com" or "@ldstrong.com." It's easy to miss a small change like this, especially if the email's displayed name matches your expectations.
Recognizing a Spoofed Email
In 2019, Statista found that the average office worker received over 120 emails a day. While many of those won't arouse suspicion, it's crucial that you ingrain the warning signs into your brain. That way, you can quickly recognize a spoofed email even if you're not actively searching.
The biggest red flags for a spoofed email include:
- A mismatched display name and email: This is a strong sign of display name spoofing. Pay special attention to the email domain to see if it's been slightly altered from the original.
- Feeling pushed to click on a link or attachment: Email spoofing is a form of social engineering. It takes advantage of your trust in a relationship to coax you into downloading malware or giving away information.
- The signature information appears unprofessional or incorrect: Hastily produced messages often have unprofessional language or spelling errors. This fact becomes more apparent as the content becomes more specific.
- Replies aren't sent back to the original sender: Spoofers often change the reply address because the sender's email isn't part of a legitimate domain.
You should also remember the general signs of an email scam. Legitimate organizations will never ask you to share your login credentials, personal identifiers, or social security number over email or text. You can also scan the messages for spelling or punctuation errors if you're grammar savvy.
Recently, artificial intelligence has gotten increasingly proficient at avoiding many of the telltale warning signs of an email scam. This same technology is used legitimately to optimize the timing and frequency of a cold email, making it harder to distinguish between sophisticated outreach and strategic spoofing. It's best to start training yourself now to look further than general warning signs.
How To Protect Yourself From Email Spoofing
The best defense against email spoofing includes a combination of software and strong online habits. Cybercrime is constantly evolving, and defensive technology doesn't always keep up. Here, we'll review what you can implement today to lower your risk of falling for a fake message.
Anti-Malware
Despite the previous warning, we strongly recommend installing a robust anti-malware solution such as Norton 360 or Avira. These programs use machine learning to identify false domains and possibly harmful links.
Digital Signatures
Digital signatures are a way to protect website owners from spoofers using their domain against others. Domain Key Identified Mail (DKIM) proves that an outgoing email originated from your domain. This safety measure ensures that your business partners and professional associates won't fall for email spoofs and harm your reputation in the process.
Always Check Your Emails
Getting dozens of digital messages daily is typical, and people have gotten much better at instinctively knowing which statements are shady. But, if you ever feel like you need a little help in confirming a spoofed email, the easiest things to check are:
- What email address your reply is sent to
- If the message is asking you for personal information
- Whether the email's domain is legitimate
It's also recommended to use software and proactive habits to protect yourself. Artificial intelligence, anti-malware, and email signing are fantastic tools for passively detecting threats in your inbox. If you're still worried about what more you can do to keep yourself safe, check out the IDStrong blog for tips on staving off the day's most prominent threats!
















